Data encryption is one of the most recent lessons we learned in our Data Structures and Algorithms class. Understanding the fundamentals of Data Structures and Algorithms in this area is similar to discovering the mysteries of the digital universe. We have recently studied a number of important topics that are both fascinating and essential to the working world. Each of these subjects will be thoroughly discussed in this essay, along with their importance.
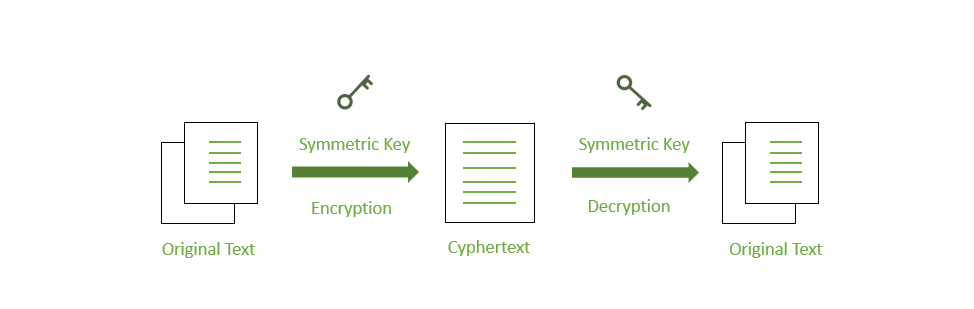
In an age where data breaches and cyberattacks are increasingly prevalent, data encryption stands as the sentinel guarding our digital fortresses. This fundamental aspect involves the art of transforming plain text into a coded form, often referred to as ciphertext, rendering it indecipherable to unauthorized eyes. This process ensures that even if unauthorized individuals gain access to encrypted data, they cannot decipher it without the decryption key. Understanding data encryption isn't just a matter of safeguarding sensitive information; it's about ensuring data integrity and authenticity across applications, from secure messaging and online banking to e-commerce and government communications. As we navigate this digital age, data encryption has become an indispensable pillar of modern technology.
Encryption ensures that sensitive information, such as personal messages, financial transactions, and medical records, remains confidential. In an era when data breaches and cyberattacks are common, the encryption of personal and sensitive data is crucial. This also safeguards against unauthorized access to data, whether it's stored on a device, transmitted over a network, or stored in the cloud. Even if an attacker breaches a system, the encrypted data remains unreadable without the decryption key. It not only protects data from unauthorized access but also verifies its integrity. Any alteration to encrypted data, even minor changes, will result in decryption failure, alerting users to potential tampering. Many industries and regulatory bodies require the encryption of sensitive data to comply with legal and industry-specific regulations. Failure to do so can result in severe penalties.
There are several types of data encryption; the caesar cipher, vigenère Cipher, and substitution cipher. For the caesar cipher, in cryptography, the study of secret messages and their applications, it is helpful to be able to switch from a string to a character array and back again. This field investigates methods for encrypting data, which transforms plaintext—the original message—into ciphertext—the scrambled version. Similarly, decryption—the process of taking a ciphertext and converting it back to plaintext—is also studied in relation to cryptography.
In order to use the Caesar cipher, each letter in a message must be replaced with the letter that appears three letters later in the alphabet for that language. As a result, in an English message, we would swap out each A for a D, a B for an E, a C for an F, and so on. Up until W, where Z is substituted, we follow this strategy. Then, we allow the substitution pattern to wrap around, changing X into A, Y into B, and Z into C.
A more sophisticated technique that employs multiple Caesar cipher shifts is the Vigenère cipher. This method makes the encryption more complex and secure than the standard Caesar cipher. It may, however, still be susceptible to some attacks.
With substitution ciphers, every character in the plaintext is replaced by a different character. 'A' could be changed to 'X,' 'B' to 'Q,' and so on. This approach is simple, but through frequency analysis—where the most prevalent characters are compared to their equivalents in the known language—it can be fairly simple to understand.
To conclude, data encryption is a fundamental idea with broad results, to sum up. Sensitive information is protected by data encryption, which also ensures data integrity and confidentiality. Different encryption techniques offer various degrees of security, including Caesar, Vigenère, and substitution ciphers.
Posted using Honouree